Broken Access Control
Sites have pages that're protected from regular visitors, i.e. only the site's admin user should ba able to access a page to manage other users. If a website visitor is able to access the protected page/pages they're not authorised to view, access control is broken.
Regular visitors being able to access protected pages leads to them accessing unauthorised functionality and/or being able to read sensitive information.
Scenario #1: The application uses unverified data in a SQL call that is accessing account information:
- pstmt.setString(1, request.getParameter("acct"));
- ResultSet results = pstmt.executeQuery( );
An attacker simply modifies the ‘acct’ parameter in the browser to send whatever account number they want. If not properly verified, the attacker can access any user’s account.
http://example.com/app/accountInfo?acct=notmyacct
Scenario #2: An attacker simply force browses to target URLs. Admin rights are required for access to the admin page.
If an unauthenticated user can access either page, it’s a flaw. If a non-admin can access the admin page, this is a flaw.
IDOR
Insecure Direct Object Reference, a way of exploiting a misconfiguration in the way user input is handled, to access resources you wouldn't normally be able to access. A type of access control vulnerability.
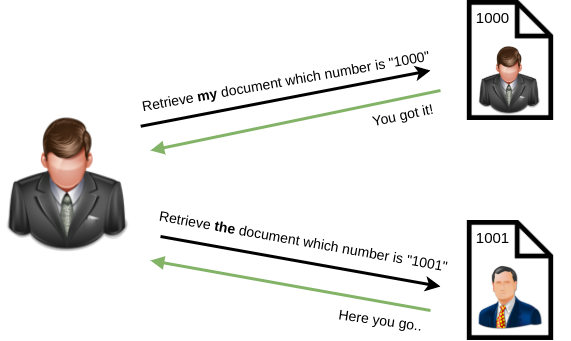
I.e. an attacker changing the value of the account_parameter in a vulnerable banking web app to access another users' information.
https://examplebank.com/account_number=1234